



Cisco
Cisco CS-BOARD55-K9 Spark Board 55 - Video conferencing Device
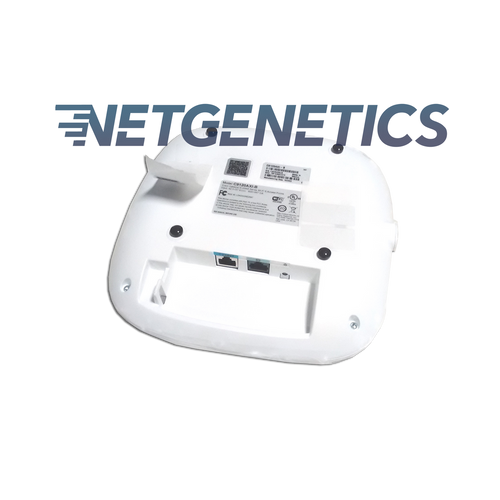
In the world of networks, there are a lot of terms that get thrown around. Access point. Router. Modem, etc. This blog will explore the difference between two standard networking terms: access poi ...
Endpoint security and cloud architecture(Post)Hackers love endpoints—those end-user devices that connect to your enterprise network. With a little ingenuity, bad actors (outside or inside your organization) can access sensitive data through empl ...
Why Organizations Should Still Care About BYOD(Post)The conversation on bring your own device (BYOD) in the workplace has been going on for a while and it’s obviously more a given in some sectors than in others. Opinions among security experts on w ...
Essential Hardware Required for a Wireless Network (Post)Specific hardware components are required for a wireless network to function. This includes a router, modem, and network adapter. A router helps connect your computer to the Internet and allows fo ...
Replacing MX204 with MX304 problems and solutions:(Post) Replacing MX204 with MX304 problems and solutions: Case study: Replacing MX204 with MX304, one 100G link wont come up Hi We've run into an issue when trying to replace ...
What is physical security?(Post)Physical security is the protection of personnel, hardware, software, networks and data from physical actions and events that could cause serious loss or damage to an enterprise, agency or institu ...
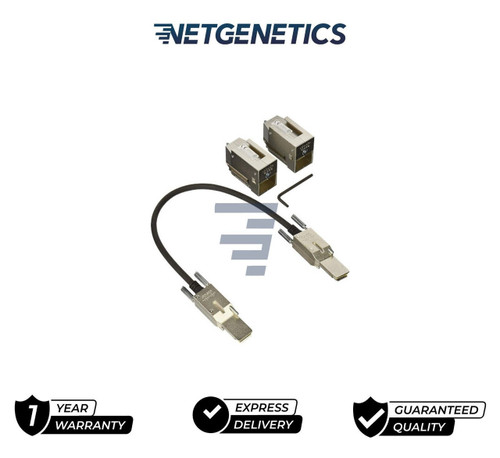
What Are SFP Ports Used For?(Post)If you know Cisco SFP Modules, you must know the SFP Ports. If you didn’t know what are SFP modules or SFP ports, you can read this article, which can tell you what are SFP ports on a Gigabit Switch ...
How to Secure Cisco Routers and Switches(Post)Routers and switches make up the bulk of network infrastructure and are vulnerable to attack. We hear about mass Denial of Service (DOS) attacks or Distributed Denial of Service (DDOS), but the ...
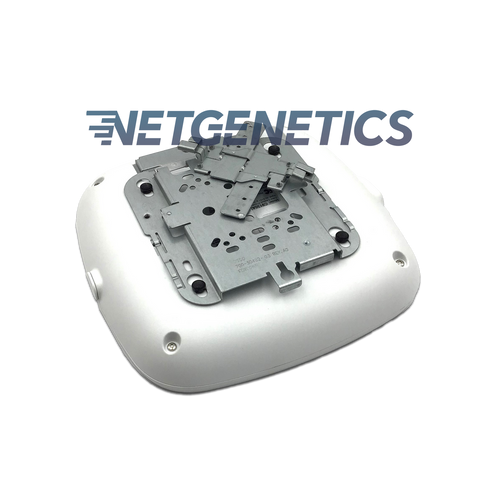
Cisco Catalyst 9130AX Series Access Points Data Sheet(Post)Cisco Catalyst 9130AX Series Access Points Data SheetThe Cisco Catalyst 9130AX Series Access Points are the next generation of enterprise access points. They are resilient, secure, and intelligent.Wi ...
What Role Does Cybersecurity Play In Your Physical Security?(Post)Today, very few organizations depend solely on one kind of security measure to secure their organization and cover their assets. Most companies employ security systems that feature physi ...
Privacy Policy Page(Page)This Privacy Policy describes how your personal information is collected, used, and shared when you visit or make a purchase from www.netgenetics.com (the “Site”). PERSONAL INFORMATION ...
N9K-C93180YC-EX(Page)



Cisco
Cisco CS-BOARD55-K9 Spark Board 55 - Video conferencing Device





Cisco
New CS-KITP60-K9 | Cisco Webex Room Kit Plus - video Conferencing



Cisco
Cisco CS-KIT-K9 Spark Room Kit with Touch 10 for Video Conferencing-CS-KIT-K9

Cisco
Cisco CS-KITPRO-P60-K9 Conference Webex Room Kit Unit Touch 10 KITPLUS


Cisco
CISCO 8865 IP Phone (CP-8865-K9=)

Cisco
NEW Cisco C9200-STACK-KIT Catalyst 9200 Series Stacking Kit

Cisco
Cisco C9200L-STACK-KIT Stacking Kit for the Catalyst 9200L Series Switches

Cisco
Cisco PWR-7201-AC 7201 AC Power Supply


Cisco
C9120AXI-A Cisco Catalyst 9120axi Wireless Access Point Bluetooth Wi-fi 6 2.4GBPS


Cisco
New Sealed Cisco C9300-NM-2Q= CISCO C9300 2x40GE (QSFP+) Module

Cisco
Cisco C9300-NM-4G - Gigabit Ethernet Network-Switch