
Dell
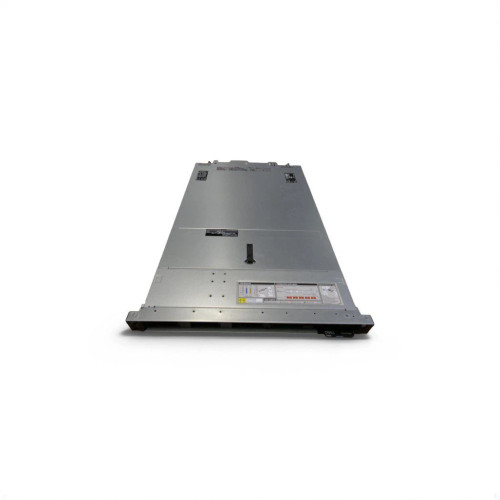
DELL R740xd 12LFF 2SFF 2x Gold 6136 512GB H730p 4xRJ45 14Caddy 2x110W Rails
Hyperconvergence combines compute, storage and networking in a single system. Enterprises can choose an integrated HCI appliance from a single vendor, or hardware-agnostic hyperconvergence softwar ...
Data Center Application Layer Attacks(Post)There have been a number of articles written on data center outages and their business costs of lost productivity, infrastructure damage, loss of brand reputation and goodwill in the marketplac ...
How are permissions managed in VMware server?(Post)Permissions are one of the most important aspects of managing VMware vCenter Server objects. Managing permissions in vCenter Server is a complex task that requires understanding both the global and l ...
What is SQL Injection (SQLi) and How to Prevent It(Post)SQL Injection (SQLi) is a type of an injection attack that makes it possible to execute malicious SQL statements. These statements control a database server behind a web application. Attackers can ...
HOW TO SECURE YOUR CISCO ROUTER USING CISCO AUTOSECURE FEATURE(Post)In today’s complex network environments securing your network routers can be a daunting task, especially when there are so many CLI commands and parameters with different security implications ...
End-of-Sale and End-of-Life Announcement for the Cisco Catalyst 3850 switches(Post)End-of-Sale and End-of-Life Announcement for the Cisco Catalyst 3850 switchesCisco announces the end-of-sale and end-of-life dates for the Cisco Catalyst 3850 switches. The last day to order the a ...
Cisco NCS-55A1-36H-S / NCS-55A1-36H-SE-S vs Arista DCS-7500R2AK-36CQ-LC(Post)Here's a polished side-by-side comparison between the Cisco NCS-55A1-36H-S / NCS-55A1-36H-SE-S and the Arista DCS-7500R2AK-36CQ-LC line card—highlighting their key distinctions, ideal use cases ...
Why Juniper MX204 is the optimal data center switch.(Post) The Juniper MX204 is a compact, high-performance router designed for service providers, enterprises, and data centers looking to optimize their network infrastructure. It offers several bene ...
The Cloud Computing Comes of Age 2019(Post)A Forrester study predicts that enterprises must respond nimbly to address changing cloud markets and technologies.Cloud computing has moved past its "self-centered teenage years" to become a "tur ...
AI: A new route for cyber-attacks or a way to prevent them?(Post)AI and machine learning are being used to fight cyber-attacks. How useful is the technology and where can it be applied? Artificial intelligence (AI) and its subset machine learning are be ...
How to Prevent XSS Attacks: What DoubleClick Advertisers Need to Know(Post)In late 2017, Google released a warning for DoubleClick platform users about a design flaw that leaves their websites vulnerable to cross-site scripting (XSS) attacks from third-party vendors.This ...
MX204 - Licensing Explanation (Post) MX204 - Licensing Explanation License tier reference: https://www.juniper.net/documentation/us/en/software/license/flex/flex-license-for-mx-series-routers-and-mpc-service- ...

Dell
DELL R740xd 12LFF 2SFF 2x Gold 6136 512GB H730p 4xRJ45 14Caddy 2x110W Rails


Dell
Dell PowerEdge R660 2x Gold 6526Y 2.8Ghz 192GB DDR5 2x 480GB NVME

Cisco
Cisco 15454-40-WXC-C ONS 15454 40Chs Wavelength Cross-Connect C-Band Module

Supermicro
Supermicro SYS-1029U-TR4T 1U Rackmout W/ X11DPU





Cisco
New Cisco C9300X-48HX-A 48-Port UPOE+ 10G Multigig (10G/5G/2.5G/1G) w/ 1100WAC-P

Cisco
Cisco C9300X-48HXN-A Catalyst 9300X 48x MultiGB UPoE+ RJ45 1x Mod Slot Switch



Cisco
Cisco C9300X-48HX-E Catalyst 48 port UPOE+ 10G/mGig Switch Network New


Cisco
Cisco C9300X-48HX-A 48-Port UPOE+ 10G Multigig (10G/5G/2.5G/1G) w/ 1100WAC-P



Cisco
REF Cisco C9300X-48HX-E Catalyst 48 port UPOE+ 10G/mGig Switch Network New


Cisco
Cisco C9300X-48HXN-A Switch – New