Categories
- Brands > Dell > Dell Workstations
- Brands > Cisco > Cisco Switches > Catalyst Switches > C9300 Series
- Brands > Dell > Dell Servers
- Brands > HPE > HPE Servers > HPE Gen 10 Servers
- Brands > Cisco > Cisco Routers > Cisco Edge Platforms
- Brands > HPE > HPE Servers > HPE Gen 11 Servers
- Brands > HPE > HPE Servers
- Brands > HPE > HPE Servers > HPE Gen 9 Servers
- All Products > Server GPUs
- All Products > Computer Workstations
- Brands > Supermicro > Supermicro RAM
- Brands > Supermicro > Supermicro Servers
Brands
Apple-
How to secure your computer from Hackers(Post)
When the glossy sheen of the World Wide Web started to dull – sometime in the mid-to-late 1990s – computer users were beginning to witness the downside of connectivity, and they did not like what ...
The Cloud Computing Comes of Age 2019(Post)A Forrester study predicts that enterprises must respond nimbly to address changing cloud markets and technologies.Cloud computing has moved past its "self-centered teenage years" to become a "tur ...
Virginia Attorney General’s Office Struck by Cyberattack Targeting Attorneys’ Computer Systems(Post)Virginia Attorney General’s Office Struck by Cyberattack Targeting Attorneys’ Computer Systems The Virginia Attorney General’s office, the state’s top pros ...
Confidentiality Privacy and Security over Internet(Post)Privacy `Privacy' is a vaguely defined term that, in an online context, includes the right of an individual to: Determine what information is collected about them and how it is ...
What is Air Gap Defence Technology and How Does it Affect Me?(Post)As technology evolves around us, so unfortunately do the clever criminals who exploit it. I am not a cyber-security expert, but I move in the IT consultancy circles and have many friends who ar ...
The business of hackers for hire threat actors(Post)Cybercrime has entered a new era where people don't steal just for the thrill of doing it anymore.Today’s web has made hackers’ tasks remarkably easy. For the most part, hackers don’t even have to hi ...
Cisco ASR 9000 Reloaded For Mass Scale Networking(Post)The wide-spread adoption of the Internet is simply phenomenal. 2018 marks the year where the number of Internet users has surpassed half of the world’s population with 3.6B users. And, according to C ...
What is Cyberwar?(Post)Cyberwarfare refers to the use of digital attacks -- like computer viruses and hacking -- by one country to disrupt the vital computer systems of another, with the aim of creating damage, death an ...
The US Economy and Its Impact on the Technology Sector(Post)For the most part, 2018 was a solid year for the American economy with its gears grinding on most of its cylinders. The spending of consumers increased and companies had more investments. But the ...
Cisco to deliver its first server for artificial intelligence and machine learning workloads(Post)Cisco has unveiled a new version of Cisco UCS, its first server designed specifically for artificial intelligence (AI) and machine learning (ML) workloads.In a statement on Monday, the firm said t ...
Top 10 Most Common Types of Cyber Attacks(Post)A cyber attack is any type of offensive action that targets computer information systems, infrastructures, computer networks or personal computer devices, using various methods to steal, alter or ...
What is hyperconvergence?(Post)Hyperconvergence combines compute, storage and networking in a single system. Enterprises can choose an integrated HCI appliance from a single vendor, or hardware-agnostic hyperconvergence softwar ...
-


Juniper
Juniper ACX7100-48L-DC-AO NewJuniper Overview The Juniper Networks ACX7100-48L Cloud Metro Router is a fixed-configuration, high-performance router, featuring a 1-U form factor that provides high port density,... -
Add to Cart Nvida-Mellanox
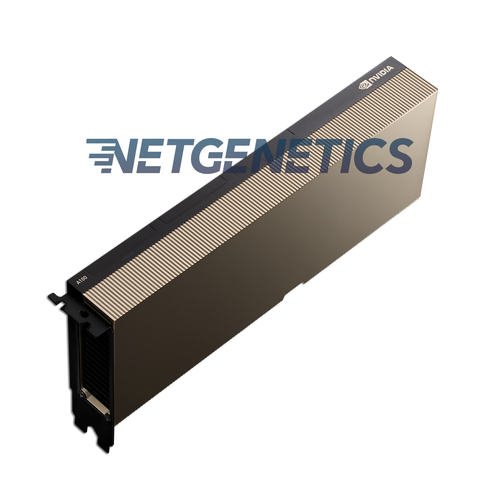
NEW NVIDIA Tesla A100 80GB GPU PCIe Deep seek Learning AI Computing Graphics CardNvidia A100 80GB Tensor Core GPU The Nvidia A100 80GB accelerator is built on the groundbreaking Ampere computing architecture, delivering unprecedented performance for demanding AI, data analytics,...$18,500.00 -

Add to Cart -

Add to Cart -

Add to Cart -



Add to Cart Dell
Dell PowerEdge XR5610 Server , Bare Metal dual ACDell PowerEdge XR5610 Server - support@netgenetics.com Dell Technologies Dell PowerEdge XR5610 Server is a rugged, high-performance server built for edge computing and demanding...$4,995.00 -

Add to Cart Supermicro
Supermicro SYS-2029TP-HC1R 2U NODE - 2TB DDR4Supermicro SYS-2029TP-HC1R 2U NODE - 2TB DDR4 Overview The Supermicro 2TB Node for the SYS-2029TP-HC1R is a powerful and scalable compute solution built to deliver maximum performance for...$5,799.00 -



Choose Options Cisco
New Cisco AIR-AP1832I-B-K9C Mobility Express Wireless Access PointAIR-AP1832I-B-K9C-New OverviewAIR-AP1832I-B-K9C is one of the Cisco Aironet 1830 Series Access Points. Cisco 1830 AP series is ideal for small and medium-sized networks. This series supports the...$325.00 -

Add to Cart Supermicro
Supermicro SYS-2029TP-HC1R 2U NODE - 512GB DDR4Supermicro SYS-2029TP-HC1R 2U NODE - 512GB DDR4 Overview The Supermicro 512GB Node for the SYS-2029TP-HC1R is a high-performance compute node designed to maximize the power, scalability, and...$3,999.00 -



Add to Cart Dell
Dell PowerEdge XR5610 Server - 1 x Gold 6421N, 64GB, 2 x 600GB HDDs 1RU CustomizeDell PowerEdge XR5610 Server - 1 x Gold 6421N, 64GB, 2 x 600GB HDDs 1RU Call: 877-263-8436 to customize your build. Dell Technologies Dell PowerEdge XR5610 Server is a rugged, high-performance...$7,999.00 -

HPE
HPE ProLiant DL385 Gen11HPE ProLiant DL385 Gen11 - Ask for Quote Overview The HPE ProLiant DL385 Gen11 server is a 2U 2P solution that delivers exceptional compute performance, upgraded high-speed data transfer rate and...$9,399.00 -

HPE
HPE ProLiant DL360 Gen11HPE ProLiant DL360 Gen11 - Ask for Quote Overview The HPE ProLiant DL360 Gen11 server is a rack-optimized, 1U 2P solution that delivers exceptional compute performance, upgraded high-speed data...$4,399.00
