-
Why Organizations Should Still Care About BYOD(Post)
The conversation on bring your own device (BYOD) in the workplace has been going on for a while and it’s obviously more a given in some sectors than in others. Opinions among security experts on w ...
8 Different Types of Malware(Post)1. VirusWe tend to refer to all malware as viruses, but it’s not so. A virus modifies other legitimate host files in such a way that when you execute a file in the victim’s system, you also execut ...
How to Have Control Over Your Online Information(Post)In the ancient times the power sources in the world were explained through the four elements: earth, air, fire, and water. In the modern times, anecdotally (or not) it has been added a fifth on ...
How to Prevent DDoS Attack in 2019(Post)The first known DDoS attack was carried out in the year 2000 by a 15-year-old boy named Michael Calce, according to Norton, and was used to temporarily bring down huge websites like Yahoo, CNN, an ...
How AI and intelligent automation are being leveraged to boost network performance (Post) Imagine networks that can self-adjust their coverage and capacity where it’s needed, when it’s needed. Networks that can heal themselves when things go wrong, and optimize for su ...
Six ways to improve data lake security(Post)Data lakes, such as Oracle Big Data Service, represent an efficient and secure way to store all of your incoming data. Worldwide big data is projected to rise from 2.7 zettabytes to 175 zettabytes by ...
How to Prevent XSS Attacks: What DoubleClick Advertisers Need to Know(Post)In late 2017, Google released a warning for DoubleClick platform users about a design flaw that leaves their websites vulnerable to cross-site scripting (XSS) attacks from third-party vendors.This ...
OWASP Top 10 Security Risks – Part I(Post)OWASP stands for the Open Web Application Security Project, an online community that produces articles, methodologies, documentation, tools, and technologies in the field of web application securi ...
OWASP Top 10 Security Risks – Part II(Post)The OWASP Top 10 list consists of the 10 most seen application vulnerabilities: InjectionBroken AuthenticationSensitive data exposureXML External Entities (XXE)Broken Access controlSecurity misco ...
What are the differences between N9K-C93180YC-FX3 vs N9K-C9348GC-FX3(Post)What are the main differences and the similarities between the Cisco Nexus N9K-C93180YC-FX3 vs N9K-C9348GC-FX3 Side by side comparison: The Cisco N9K-C93180YC-FX3 and N9K-C9348GC-FX3 ...
-

Choose Options Cisco
New Arista QSFP-100G-SWDM4 100GBASE-SWDM4 70m OM3/100m OM4 Duplex MMF QSFPNew Arista QSFP-100G-SWDM4 100GBASE-SWDM4 70m OM3/100m OM4 Duplex MMF QSFP Overview The Arista QSFP-100G-SWDM4 is a 100GBASE-SWDM4 transceiver designed for high-speed data transmission over duplex...$199.00 -



Choose Options Cisco
New Cisco ISR4461/K9 Integrated Services 4461 RouterNew Cisco ISR4461/K9 Integrated Services 4461 Router Product overview The Cisco ISR4461/K9 router is a membrer of the Cisco 4000 ISR Family Integrated Services Router (ISR) revolutionizes WAN...$5,999.00 -


Choose Options Cisco
Cisco ISR4461/K9 Integrated Services 4461 RouterCisco ISR4461/K9 Integrated Services 4461 Router Product overview The Cisco ISR4461/K9 router is a membrer of the Cisco 4000 ISR Family Integrated Services Router (ISR) revolutionizes WAN...$850.00 -

Choose Options Cisco
Arista QSFP-100G-SWDM4 100GBASE-SWDM4 70m OM3/100m OM4 Duplex MMF QSFPArista QSFP-100G-SWDM4 100GBASE-SWDM4 70m OM3/100m OM4 Duplex MMF QSFP Overview The Arista QSFP-100G-SWDM4 is a 100GBASE-SWDM4 transceiver designed for high-speed data transmission over duplex...$59.00 -


Choose Options Cisco
Cisco C9300L-24P-4X-A 24x 1GB PoE+ RJ-45 4x 10GB SFP+ SwitchCisco C9300L-24P-4X-A 24x 1GB PoE+ RJ-45 4x 10GB SFP+ Switch Overview The Cisco Catalyst C9300L-24P-4X-A is a stackable enterprise switch designed for security, IoT, mobility, and cloud...$1,650.00 -


Add to Cart Cisco
CISCO EPA-1X100GE ASR1000 1X100GE Ethernet Port AdapterCisco EPA-1X100GE ASR 1000 Series 1x 100GB CPAK Router Port Adapter Overview The Cisco EPA-1X100GE is a fixed port Ethernet line cards for the Cisco ASR 1000 Series Aggregation Services...$4,999.00 -

Choose Options Cisco Meraki
Cisco Meraki MS350-24P-HW 24x 1GB PoE RJ-45 4x 10GB SFP+ Unclaimed SwitchCisco Meraki MS350-24P-HW 24x 1GB PoE RJ-45 4x 10GB SFP+ Unclaimed Switch Overview The Cisco Meraki MS350-24P-HW is a cloud-managed, Layer 3, 24-port Gigabit Ethernet switch designed for...$495.00 -

Choose Options Cisco
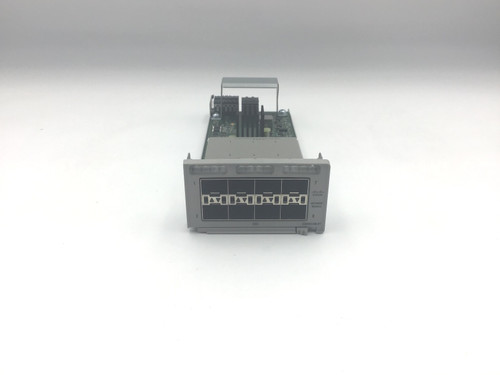
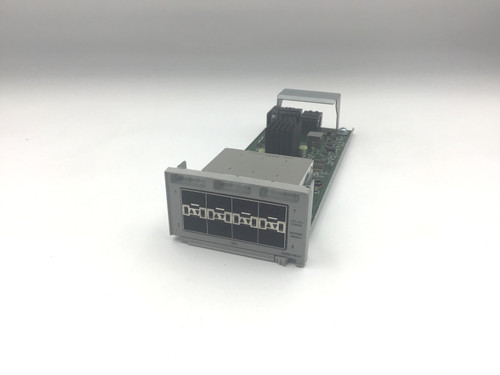
Cisco C9300X-NM-8Y Catalyst 9300X Series 8x 25GB SFP28 Switch ModuleOverview The Cisco C9300X-NM-8Y is an uplink expansion module for Cisco Catalyst 9300X Series switches. It provides eight SFP28-based uplink ports that support 1G, 10G, and 25G Ethernet...$799.00 -


Add to Cart Dell
Dell N1524P 0GCXM N1500 Series 24x 1GB PoE+ RJ-45 4x 10GB SFP+ EMC SwitchDell N1524P 0GCXM N1500 Series 24x 1GB PoE+ RJ-45 4x 10GB SFP+ EMC Switch Overview The N1524P switch series offers a power-efficient Gigabit Ethernet (GbE) network-access solution with integrated...$199.00 -


Add to Cart Ubiqiti Wireless
Ubiquiti ER-8-XG EdgeRouter 8x 10GB SFP+ 1x 1GB RJ-45 RouterUbiquiti ER-8-XG EdgeRouter 8x 10GB SFP+ 1x 1GB RJ-45 Router Overview The Ubiquiti ER-8-XG EdgeRouter provides 8x 10 Gigabit Ethernet SFP+ ports and a single 1 Gigabit Ethernet RJ-45 port. It...$1,999.00 -

Add to Cart Cisco
Cisco C1000-48T-4X-L Catalyst 1000 48x 1GB RJ45 4x 10GB SFP+ SwitchCisco C1000-48T-4X-L Catalyst 1000 48x 1GB RJ45 4x 10GB SFP+ Switch Overview Cisco® Catalyst® 1000 Series Switches are fixed managed Gigabit Ethernet and Fast Ethernet...$625.00 -

Add to Cart Cisco
New Cisco C1000-48T-4X-L Catalyst 1000 48x 1GB RJ45 4x 10GB SFP+ SwitchCisco C1000-48T-4X-L Catalyst 1000 48x 1GB RJ45 4x 10GB SFP+ Switch Overview Cisco® Catalyst® 1000 Series Switches are fixed managed Gigabit Ethernet and Fast Ethernet...$1,340.00
